Organization Management
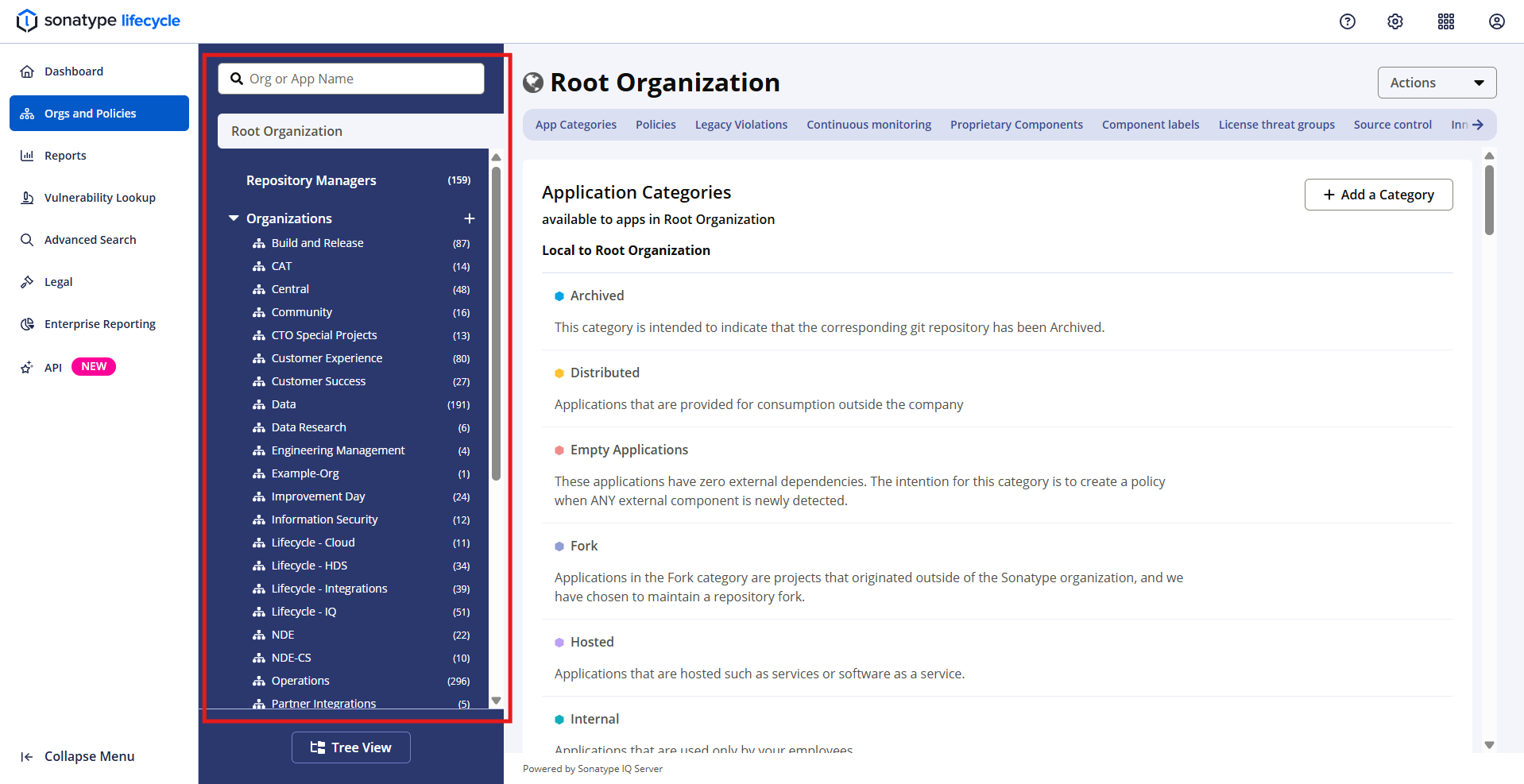
The Orgs and Policies view is designed to mimic your management hierarchy of your catalog of applications and business units.
Hierarchy And Inheritance
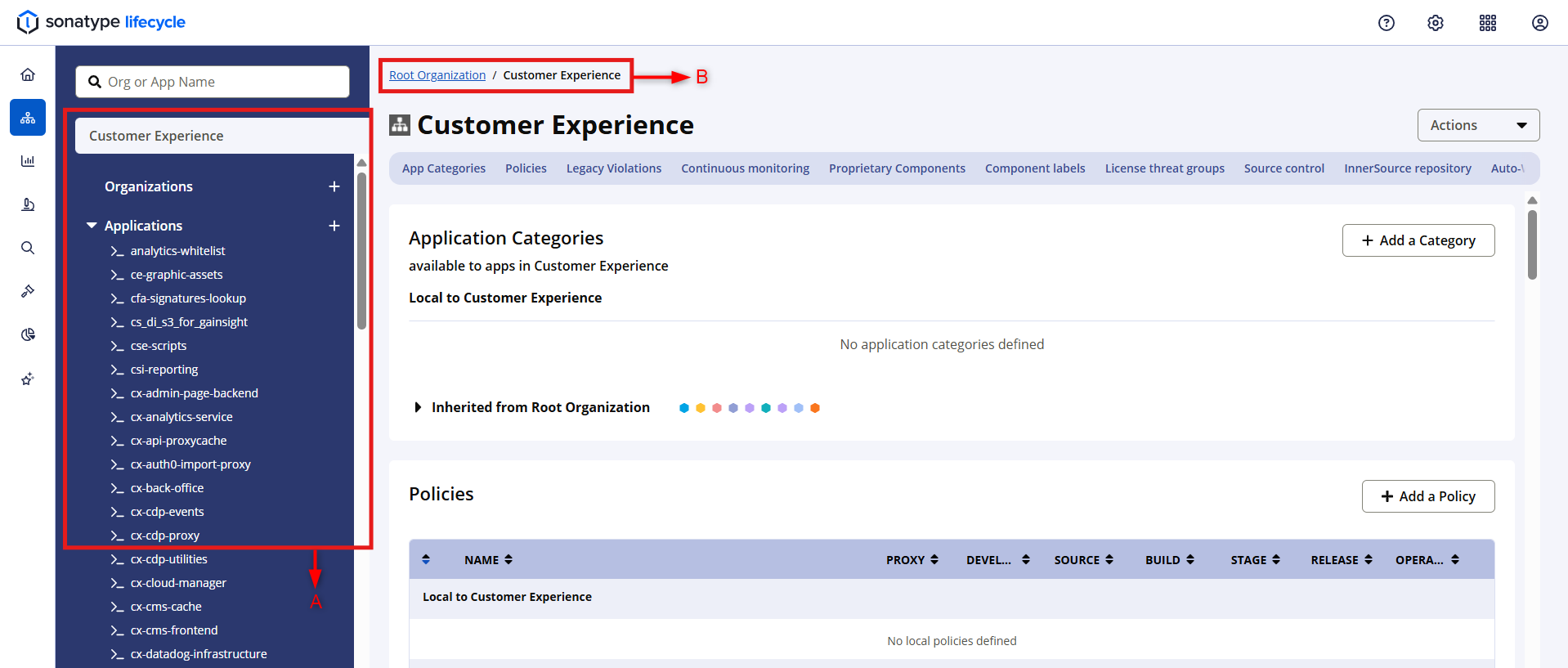
Lifecycle uses a parent-child relationship when managing organizations and applications. Applications are 'children' of organizations and organizations are the 'children' of the root organization. This is referred to as the organizational hierarchy and is used for establishing ownership and inheritance.
Inheritance refers to re-using policy and configuration defined at a higher hierarchical level. A policy defined at the root organization will be inherited by all organizational levels. Policies defined on an organization will apply to the organizations and applications descendant from it.
As a best practice we recommend setting policy at the root organization level while using application categories and overrides to scope policies to the correct applications. Alternatively we recommend setting access controls to the organization level to limit access to only that which the users is a stakeholder of.
Root Organization
The Root Organization is an entity at the top of the system hierarchy that allows you to set policy globally across all organizations and applications.
Multi-level Hierarchy Model
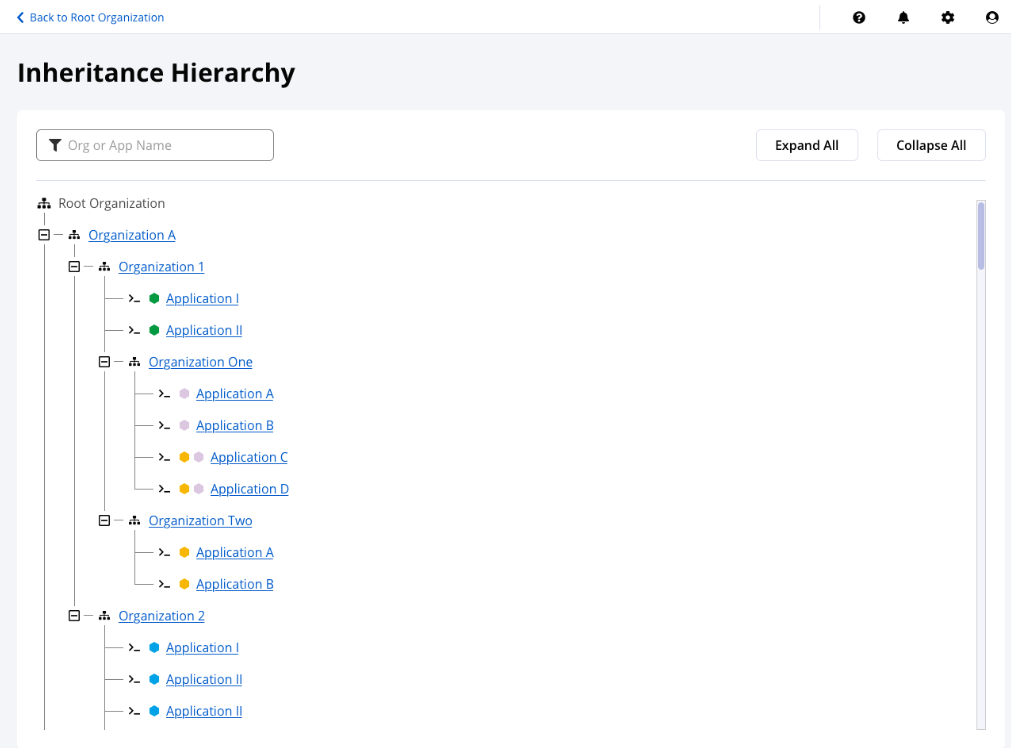
Sonatype Lifecycle supports a multi-level organization hierarchy model, consisting of a top-level organization (Root Organization) linked with organizations at multiple lower levels.
This model provides flexibility when distributing the organizational structure for application ownership to mimics the management hierarchy of your organization's business model. This decentralizes and distributes managing policies among lower organizational levels.
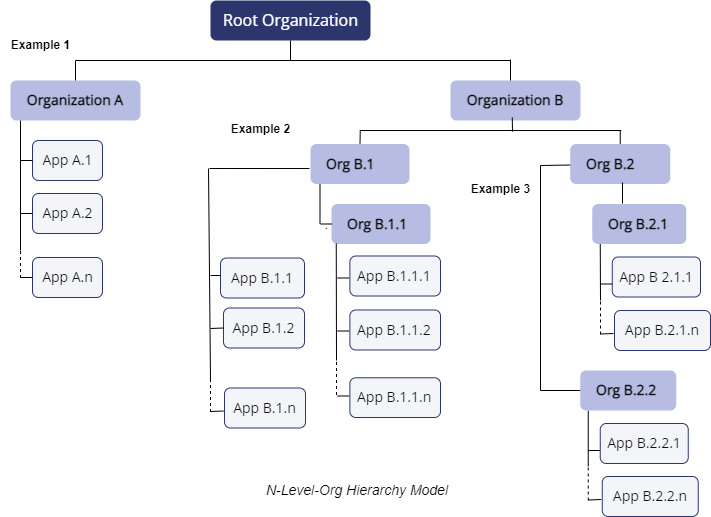 |
Organization A owns multiple applications
Organization B sets policy and administers 2 sub-organizations
Org B.1 is responsible for the team Org B.1.1 and owns 3 applications as well.
Org B.2 manages 2 teams each with their own applications
Use case scenarios
Match the organizational hierarchy of different business units
Report on the risk profile of applications specific to a business unit
Apply policy to specific teams and groups of applications
Decentralize access control to individual business units
Support micro-services type architecture by grouping applications