Advanced Search
Use the Advanced Search feature to search the configuration and component details from the UI.
Repository Firewall
The Advance Search does not provide results for Repository Firewall components. Use the Firewall Dashboard to search for quarantined components.
To script searches for Repository Firewall, use Firewall REST API.
Sonatype Lifecycle
The Advanced Search does not return policy violations. Use the Lifecycle Dashboard to search policy violations.
To script advanced searches for Lifecycle, use Advanced Search REST API.
This feature is enabled by default with the search index created automatically. The search index may be manually recreated by the System Administrators from the System Preferences menu. Select the enabled checkbox before creating the index. The last indexed time displays once the index has successfully been created.
Automatic Re-indexing
The Advanced Search automatically re-indexes when changes are made to the data. Automatic indexing only applies to data changes made while the feature is enabled.
Search Performance
Advanced Search feature retrieves results from large data sets. To limit risk to the performance of the server by consuming too much of the service resources, limits to the query results are in place. You will see an error message asking you to narrow down the search when this occurs.
Exporting Advanced Search Results
You may export the results of an advanced search by selecting the Export Results button from the Advanced Search page. The search results are downloaded in a CSV file.
Results may also be exported using the Advanced Search REST API.
Limitations with the Advance Search
The Advance Search does not list all vulnerabilities known to Sonatype. The complete list of vulnerabilities are stored in Sonatype's proprietary Hosted Data Services (HDS) database and is used during the application analysis.
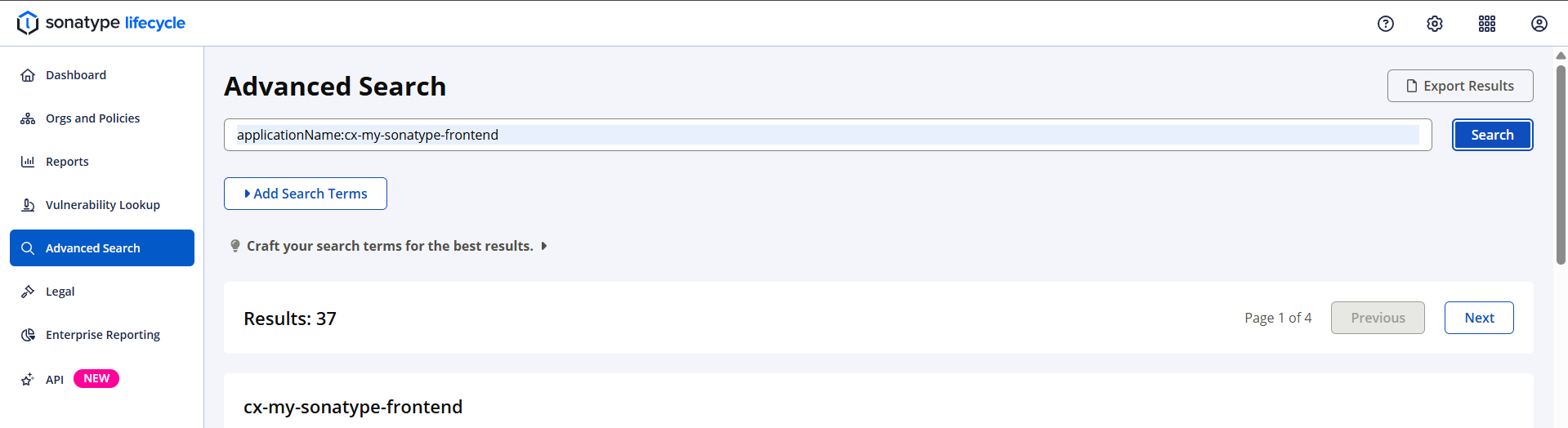
Performing a Search
Fine-tune the search query by combining multiple search terms/item types with the supported search syntax. Such queries are used to find specific organizations, applications, components, and policies by names, IDs, etc.
Steps to use Advanced Search:
Navigate to Advanced Search in the menu bar
Select the
Add Search Termsbutton to build a query and add an item typeEnter the corresponding search value to complete the search criteria
Select
Searchto view the results
Components with vulnerabilities
Selecting any search item type from the Component category will give an option to retrieve:
All components that match the search criteria
Only components that match the search criteria and have security vulnerabilities
Components from a Specific Organization
You can search for components or vulnerabilities in applications that belong to a specific organization by including the organization name or organization ID in the search query.
The search retrieves components and vulnerabilities from applications directly managed by the organization specified in the search query.
Searching into the organization hierarchy is not supported by the Advanced Search. Including an organization in the search query will not retrieve results for its child organizations.
Refer to the tables below for search item types and examples when building a search query.
Field Name | Example |
|---|---|
organizationId | organizationId:ROOT_ORGANIZATION_ID |
organizationName | organizationName:"Root Organization" |
Field Name | Example |
|---|---|
applicationId | applicationId:22951997a36045ab8593e3b6aafb9745 |
applicationName | applicationName:"My Application Name" |
applicationPublicId | applicationPublicId:MyApplicationPublicId |
applicationVersion | applicationVersion:1.0 |
sbomSpecifications | sbomSpecifications:CycloneDx |
Field Name | Example |
|---|---|
applicationCategoryId | applicationCategoryId:319cde35ef9749f4ab99a6473ad10b74 |
applicationCategoryName | applicationCategoryName:Distributed |
applicationCategoryColor | applicationCategoryColor:yellow |
applicationCategoryDescription | applicationCategoryDescription:"outside the company" |
Field Name | Example |
|---|---|
componentHash | componentHash:f5149f0aaf01daf4bb2f |
componentFormat | componentFormat:maven |
componentName | componentName:"javax.mail : mailapi : 1.4.2" |
componentCoordinateGroupId | componentCoordinateGroupId:commons-fileupload |
componentCoordinateArtifactId | componentCoordinateArtifactId:mailapi |
componentCoordinateVersion | componentCoordinateVersion:1.2.16 |
componentCoordinateClassifier | componentCoordinateClassifier:dist |
componentCoordinateExtension | componentCoordinateExtension:jar |
componentCoordinateName | componentCoordinateName:"org.webjars bootstrap" |
componentCoordinateQualifier | componentCoordinateQualifier:cp37-cp37m-win32 |
componentCoordinatePackageId | componentCoordinatePackageId:loadash |
componentCoordinateArchitecture | componentCoordinateArchitecture:x86_64 |
componentCoordinatePlatform | componentCoordinatePlatform:ruby |
Field Name | Example |
|---|---|
componentLabelId | componentLabelId:0d3f4015332e4b298ac1ed95c12ff3a3 |
componentLabelName | componentLabelName:Architecture-Cleanup |
componentLabelColor | componentLabelColor:orange |
componentLabelDescription | componentLabelDescription:"relics of a build" |
Field Name | Example |
|---|---|
policyId | policyId:b4ca64a8b8264f03b65127016859b2a2 |
policyName | policyName:Component-Unknown |
policyThreatCategory | policyThreatCategory:security |
policyThreatLevel | policyThreatLevel:10 |
Field Name | Example |
|---|---|
reportId | reportId:a6860277aa844ab5af8bfef041f7e6e5 |
policyEvaluationStage | policyEvaluationStage:Build |
vulnerabilityId | vulnerabilityId:CVE-2014-3625 |
vulnerabilityStatus | vulnerabilityStatus:Open |
vulnerabilitySeverity | vulnerabilitySeverity:7.1 |
vulnerabilityDescription | vulnerabilityDescription:"directory traversal" |