Working with Vulnerability Data
The vulnerability data is available on the Application Composition Report.
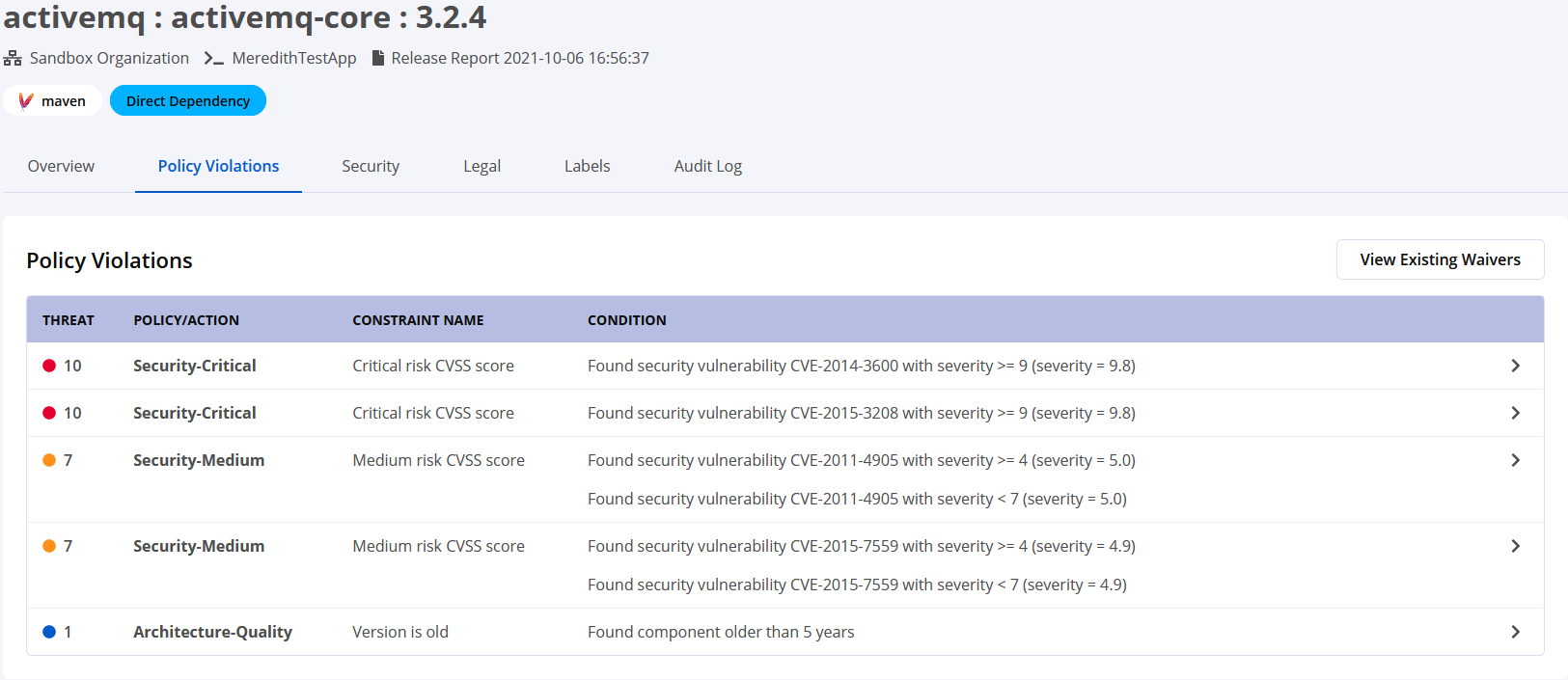
Component Details Page
In the Application Composition Report, select the violation that you are investigating to open the Component Details Page. Within the Component Details Page, select the Policy Violations tab to view the list of violations for this component.
Select a security policy violation to open the Violation Details tile, then scroll down to access the violation details.
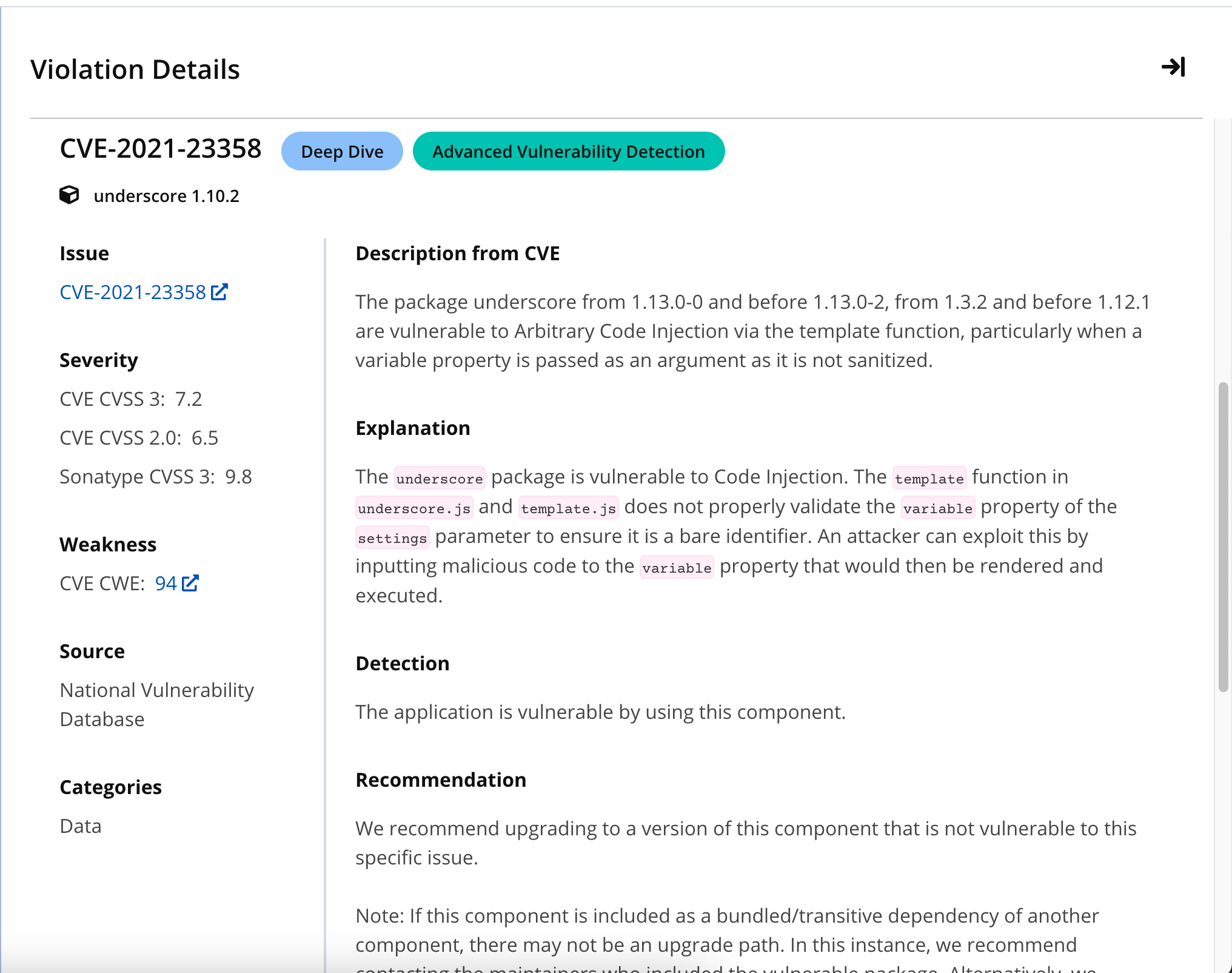
 |
The label Deep Dive indicates that this vulnerability data includes details and recommendations from the Sonatype Research Team.
The label Advanced Vulnerability Detection indicates that this vulnerability has been detected in entire files and embedded dependencies, typically beyond the public feeds.
 |
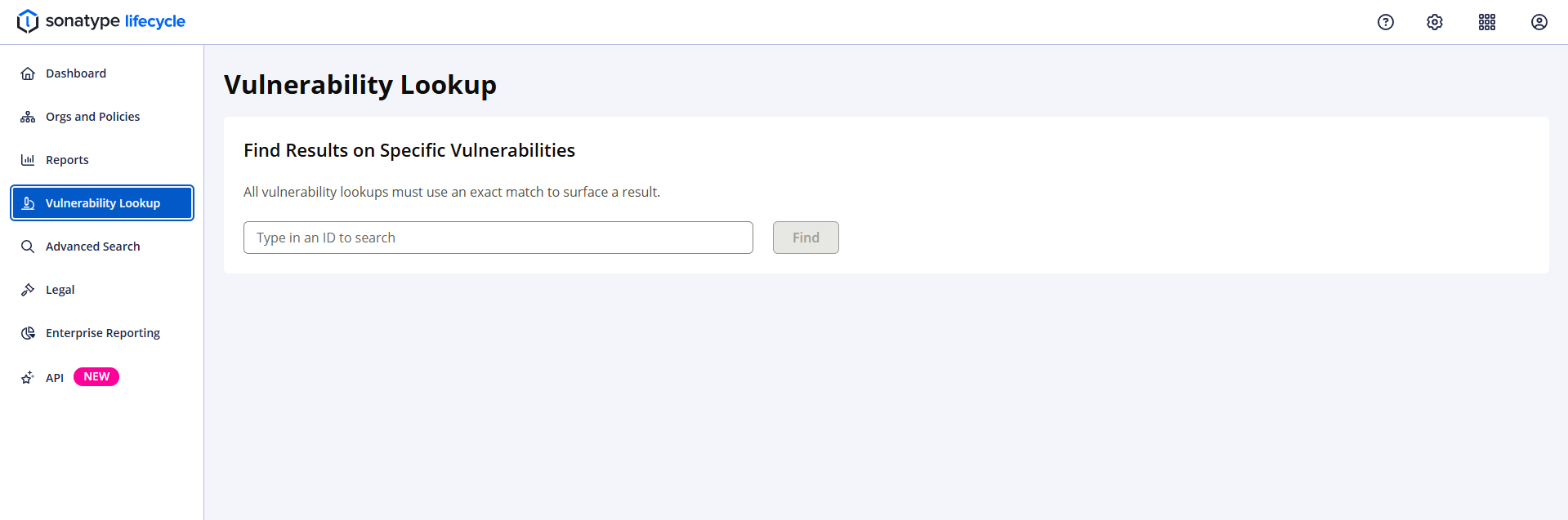
Vulnerability Lookup
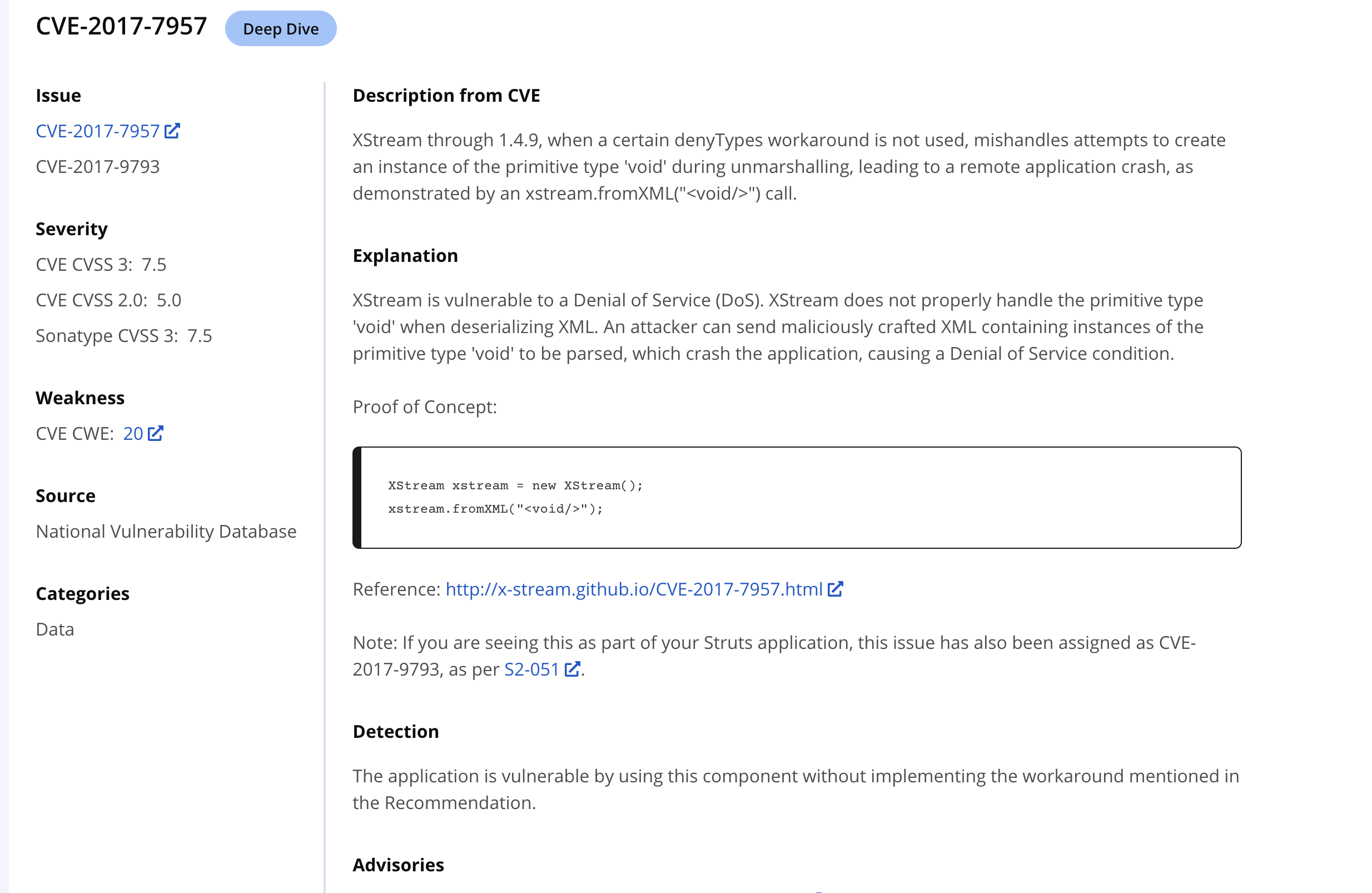
From the Vulnerabilities list, you can access detailed information on a given vulnerability by clicking the Vuln ID.
 |
The Vulnerability Lookup page can also be accessed by selecting Vulnerability Lookup from the IQ Server toolbar: