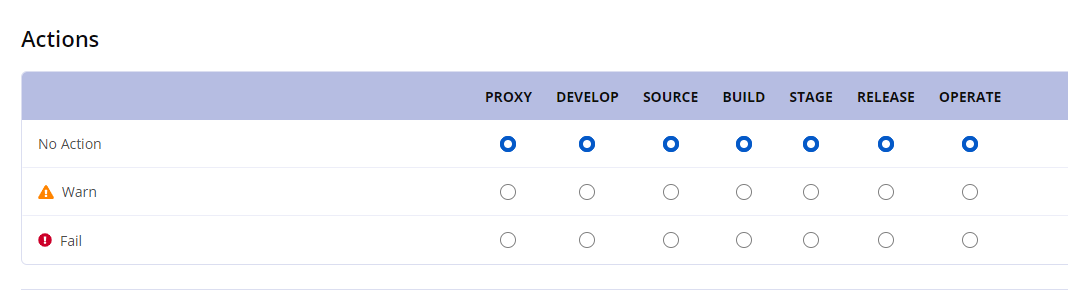
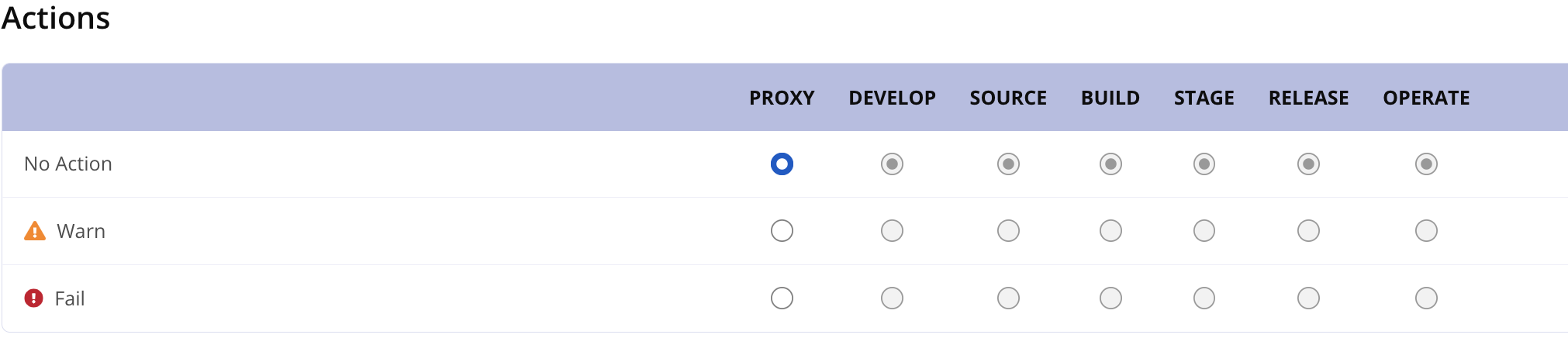
Policy Actions
Policy actions allow you to designate an action to take when violations occur at a particular stage in the development lifecycle. For each stage, you can assign one of the following actions:
No Action - This is the default setting.
Warn - Policy violations are worthy of a warning.
Fail - Policy violations are severe enough to potentially halt the development lifecycle.
If Sonatype Lifecycle is integrated with a third-party external tool, the action selected can have a direct effect on the tool. When an external tool requests a policy evaluation (of an application, repository, or component), IQ Server provides policy violation information along with the action, which the tool may (or may not) implement. For example, if you set the Build stage to Fail in a policy, a CI tool (such as Bamboo, Jenkins, or Hudson) may stop the build of an application when that policy is violated. Similarly, in a different tool, if you set a stage to Warn, a warning message may be displayed or logged in a file when policy violations occur. For more details on using actions, see Usage Suggestions for Each Stage.
To add actions to a policy:
In the Organization & Policy area, create a new policy or open an existing one for repositories or an organization or application.
In the Policy editor, click the Actions button to scroll to the Actions section.
Click the desired action — No Action, Warn, or Fail —at specific stage(s). In case of repositories, actions can be set only for the Proxy stage.
Click Update (or Create) to save the policy.
Actions at root organization or organization or application level
 |
Actions at Repositories level
 |
Usage Suggestions for Each Stage
Sonatype provides various tools and plugins to enable policy evaluation during each stage of the development lifecycle:
CLI
Maven plugin
Sonatype Repository Firewall
IDE plugins
CI plugins
Stage | Usage Suggestion |
|---|---|
Proxy |
|
Develop |
|
Source |
|
Build |
|
Stage Release |
|
Release |
|
Operate |
|
Note
The 'warn' and 'fail' actions are intended to be used by other tools that integrate with IQ Server (e.g., CI/CD platforms and deployment tools). These actions provide instructions to those tools on how to respond to policy violations. If there is no other tool involved, or if the tool is not configured to respond to these actions, then the actions will have no direct effect. This applies to all stages.