Automatic Quarantine Release
With this feature, you may configure quarantined components to be released when components no longer have failing violations. Auto-release will monitor components quarantined in the last 14 days. When new information resolves the policy violation that caused the quarantine, the component is automatically released from quarantine.
After 14 days, the component may still be released manually. However, the value of releasing that component drops dramatically, since a different component may be in place, or the component is no longer required.
Auto-Release Dashboard
The Auto-Release Dashboard displays an activity summary and components that have been auto-released from quarantine.
This view is accessed from the Firewall Dashboard.
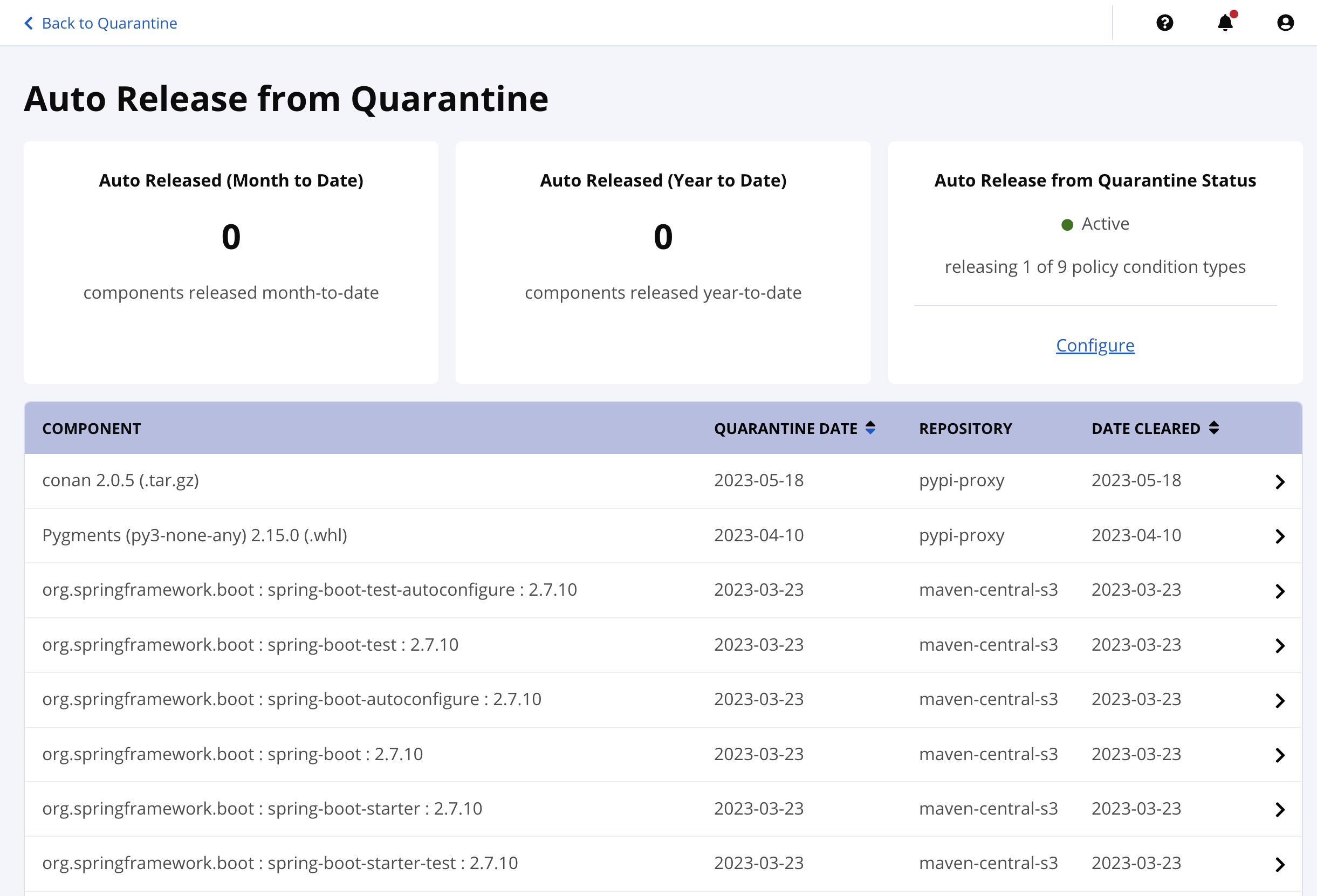
Auto-Released (Month to Date)
Components auto-released from quarantine in the current month
Auto-Released (Year to Date)
Components auto-released from quarantine in the current year
Auto-Release from Quarantine Status
Summary and configuration of policy condition types enabled for auto release from quarantine.
Component View
These are the components that were auto-released from quarantine. Selecting a row will open the Component Information Panel for that component.
These results do not include components that have been manually released from quarantine.
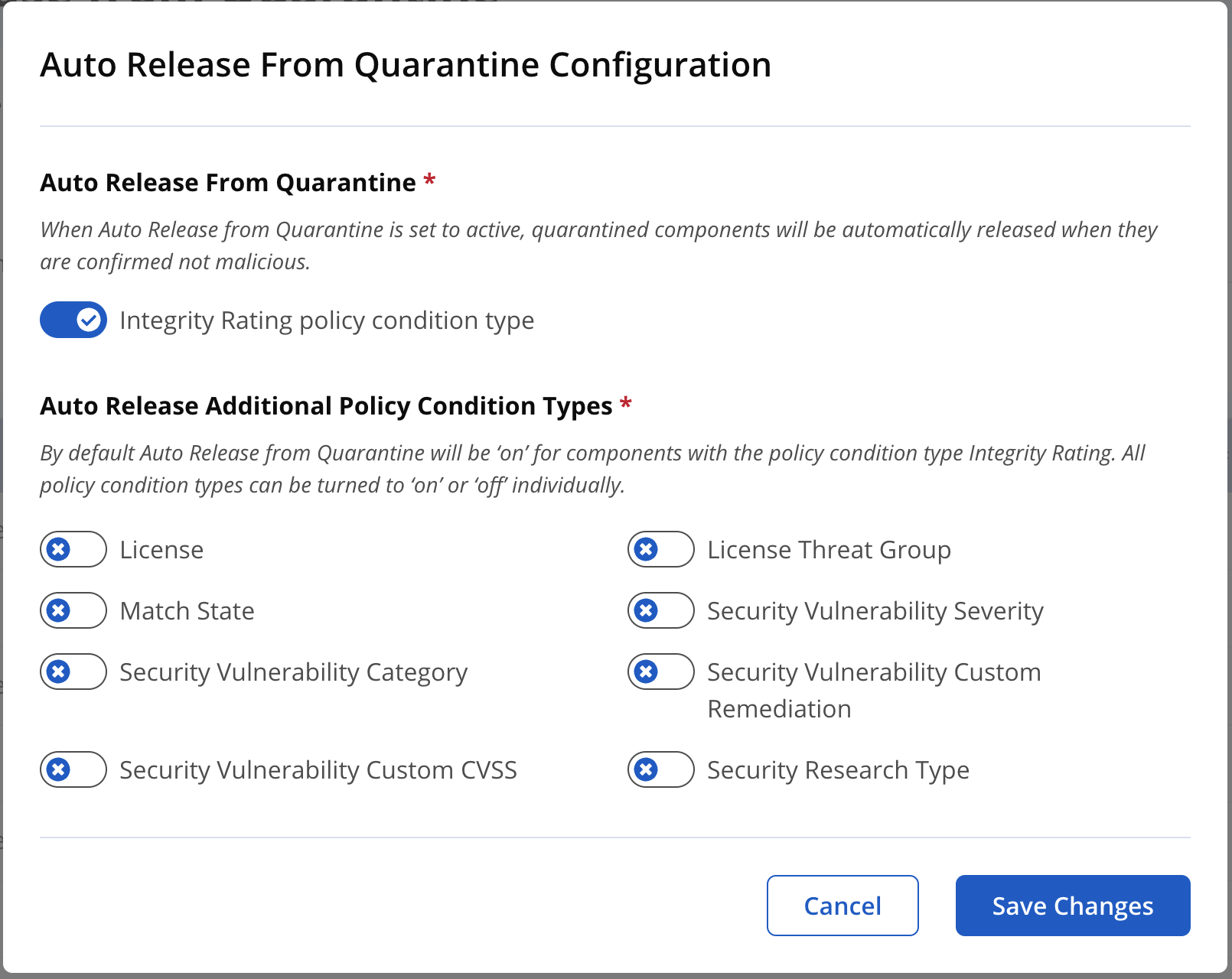
Auto Release from Quarantine Configuration
The configuration for auto-releasing quarantined components is found on the Auto Release from Quarantine dashboard.
Modifying the auto-release functionality requires the Edit IQ Elements permission set at the Repository Managers access level.
Auto-Release Task
The auto-release task runs hourly by default. The schedule interval can be configured using the following property of the Configuration REST API.
automaticQuarantineReleaseTimeIntervalInMinutes
The Re-Evaluate Repository option in the Repository Results screen will trigger the auto-release task to review quarantined components.
Policy Condition Types Supporting Auto Release
Policy violations are triggered by conditions in the policy. The condition types are used to correlate to component information.
The policy condition types that can be enabled for monitoring with auto-release from quarantine are:
Integrity Rating License License Threat Group Match State Security Vulnerability Severity Security Vulnerability Category Security Vulnerability Custom Remediation Security Vulnerability Custom CVSS Security Research Type