Dashboard
The dashboard provides the fastest way to monitor the overall health of applications you manage. It is displayed by default when you log in to Lifecycle and is also accessible from the Dashboard icon on the left navigation bar.
Dashboard is available for Lifecycle installations. To view the Dashboard, users should be assigned a Developer role for at least one application.
 |
Filters
The filters menu is accessible from the "Filter" button on the upper right side of the Dashboard as seen in the screenshot above.
You can create a customized filter to fine-tune the results displayed in the Dashboard to analyze them better.
Filter property | Description |
|---|---|
Organizations | Select the organizations for which you want to monitor violations. Selecting an organization will auto-select all organizations that are linked at lower levels in the hierarchy. You can de-select them as needed. |
Applications | Select the specific applications you want to monitor. Selecting an organization will auto-select all applications linked to it. You can de-select an application as needed. De-selecting an application will automatically de-select the organization it is linked to. |
Repositories | Select the specific repositories you want to monitor. Note: This filter is visible only in the Waivers view of the dashboard. |
Application Categories | Select the application category to view the applications for which violations have occurred. |
Stages | Select the specific DevOps stage(s) in your development cycle at which you want to view violations. |
Policy Types | Select the specific policy type(s) to view the applications it applies to. |
Violation State | Select the violation state to view corresponding application violations. |
Age | Select the time window to view the applications for which violations occurred. |
Policy Threat Level | Move the slider to set the policy threat level. This will display all violations that lie within the selected range. |
Expiration Date | Select the expiration date to view waivers that expire in the selected time period. Select "all" to include expired waivers in the search result. Note: This filter is visible only in the Waivers view of the dashboard. |
Use the Apply button to view the updated results of the filter.
To save an applied filter selection, click the Save button. Saved filters can be reused from the dropdown at the top of the sidebar.
Results
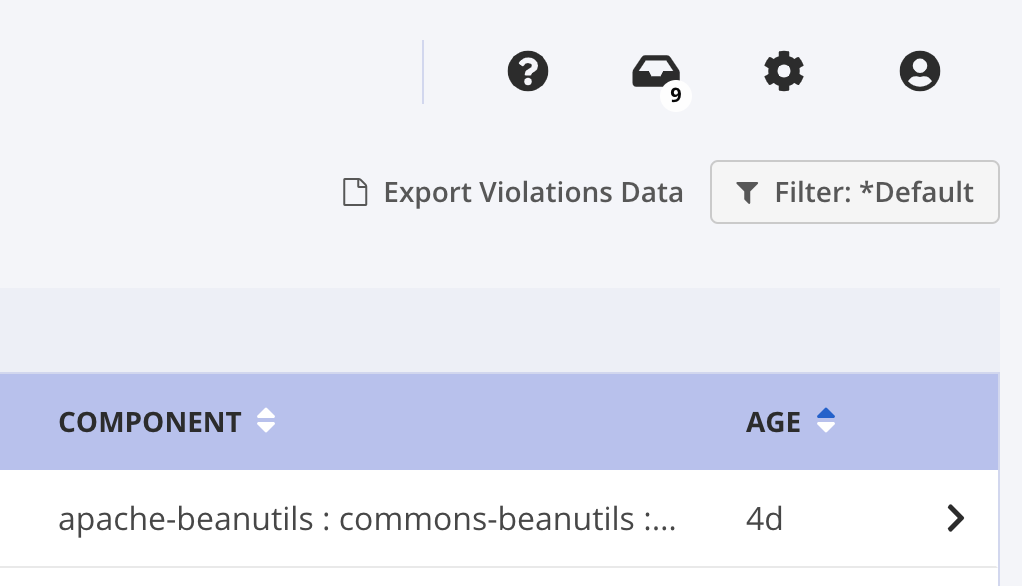
Dashboard Results display information based on applied filters. The results differ depending on the view that is currently selected.
Export the data displayed in the current results view by selecting Export Violations Data.
 |
Results are saved on your local computer as a .csv file. The first row of the .csv file contains column names.
Violations View
The Violations view is the default view for the Dashboard. It displays the policy violations found in the last 30 days, by default. You can customize the filter to view specific violations.
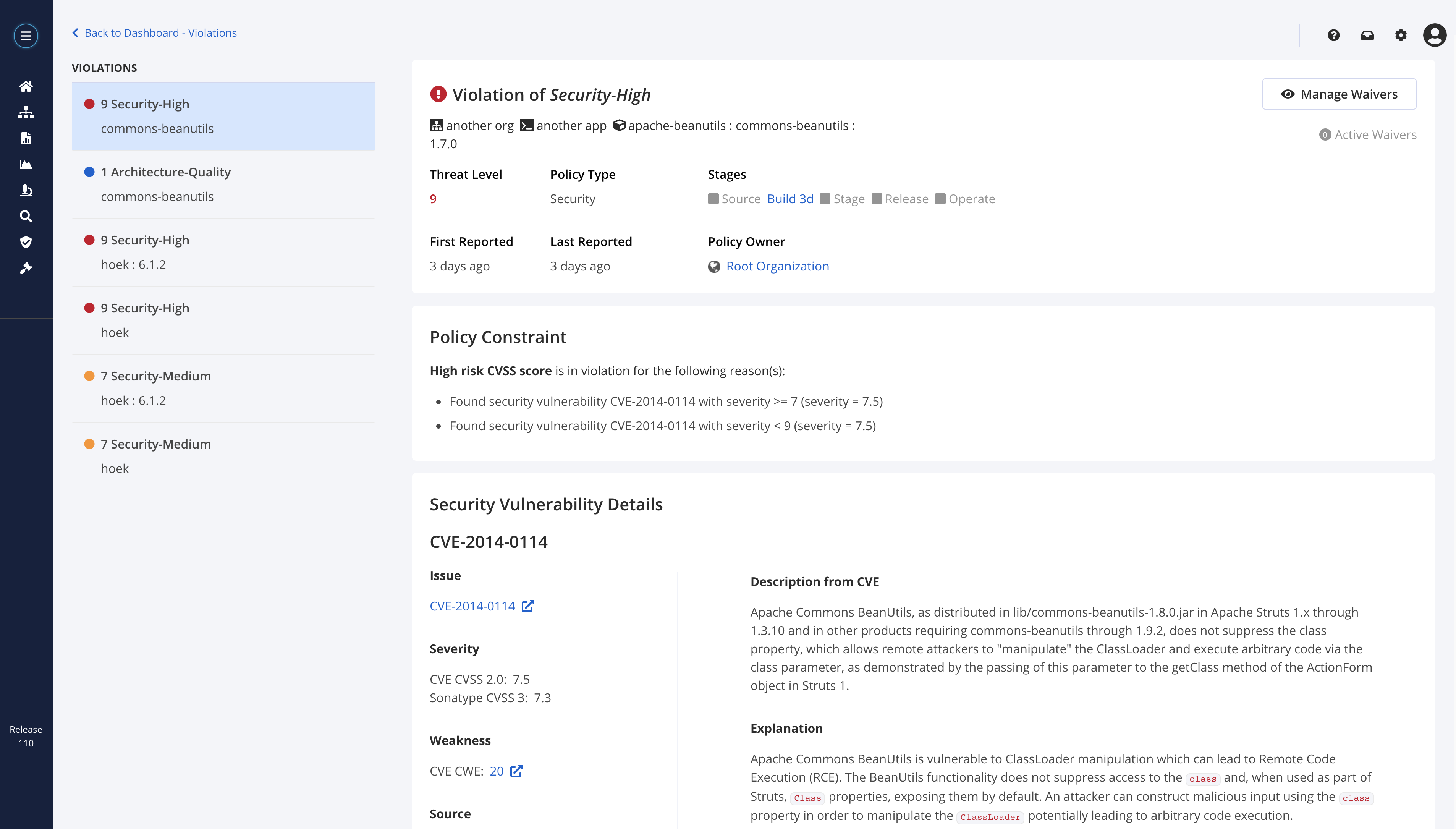
Clicking a violation in the Violations view opens the Violation Details page. The Violation Details page presents information on the violated policy, as well as the different stages of the violation that have been identified. For security violations, a detailed explanation of the vulnerability is also provided. The Manage Waivers button allows viewing, adding, and deleting waivers for selected violations.
 |
Exporting Violations Data
Column Name | Column Value |
|---|---|
Threat Level | The threat level associated with the policy violation, on a scale of 0 to 10 |
Policy Name | The name of the policy that triggered the violation |
Organization Name | Name of the organization which owns the violated policy, or is the parent of the application in which the policy was violated |
Application Name | Name of the application in which the policy violation was triggered |
Component Name | Name of the component in which the policy violation was triggered |
Date First Seen | Date in which this policy violation was first triggered for the particular component. This date is represented in ISO 8601 format. |
Timestamp First Seen | Timestamp of the date in which the policy was first triggered for the particular component. This timestamp is represented in standard unix time format. |
Reference | For security violations, the CVE or Sonatype code assigned to the vulnerability that caused the policy violation. |
Policy Violation Id | The policy violation Id that triggered the violation, useful for automation with related APIs. |
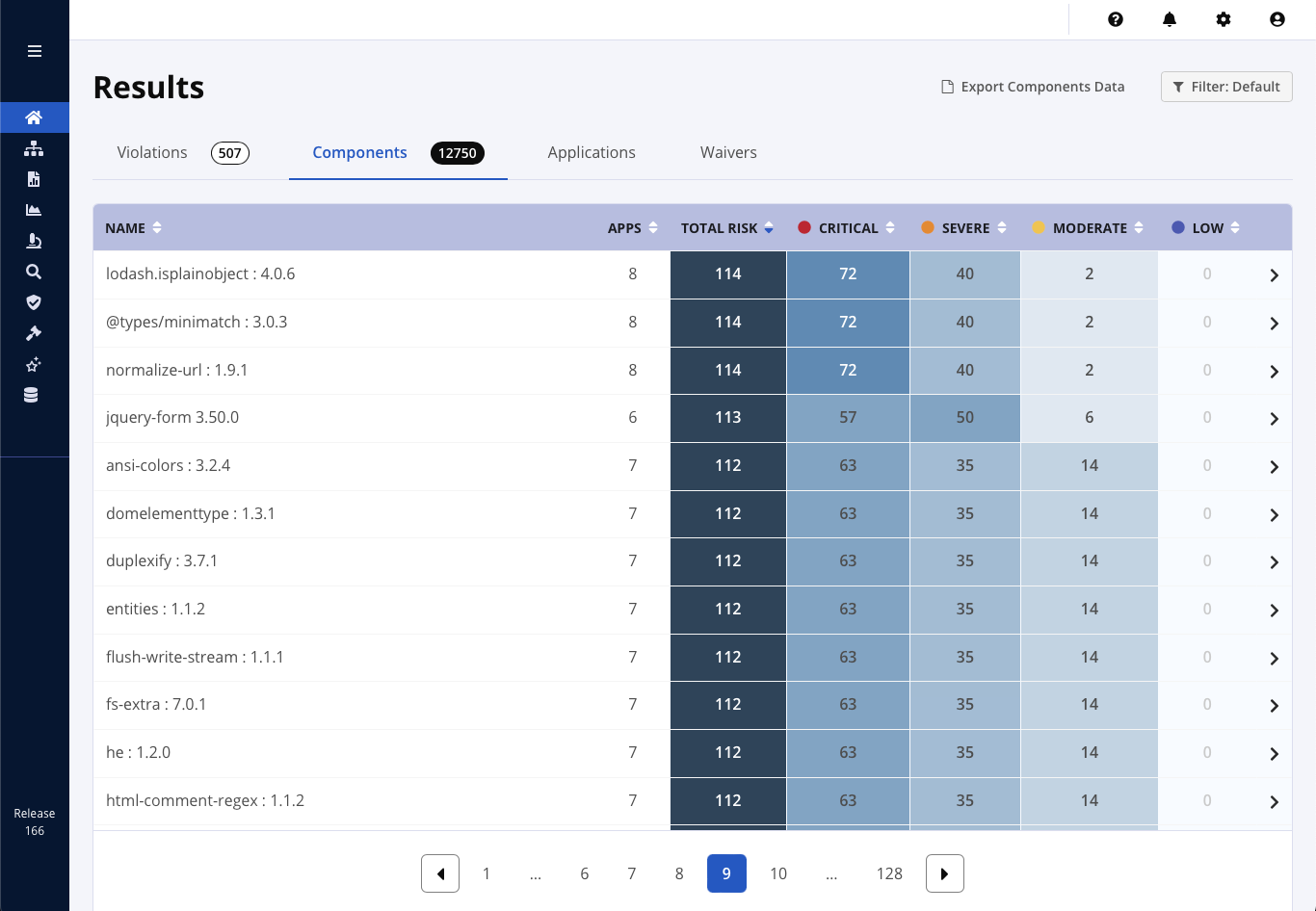
Components View
The Components view displays the implicated components based on the filters that have been set and the user's level of access.
Risk is represented in a table with the ranges of Critical, Severe, Moderate, and Low. The values represent the number of unique policy violations at that severity level. The Total Risk column is calculated by summing all the values in the row.
Clicking a component in the Components view opens the Component Risk Overview page. This page presents known coordinates for the component and all violations that have been found, organized by application. Risk information for each component is also provided:
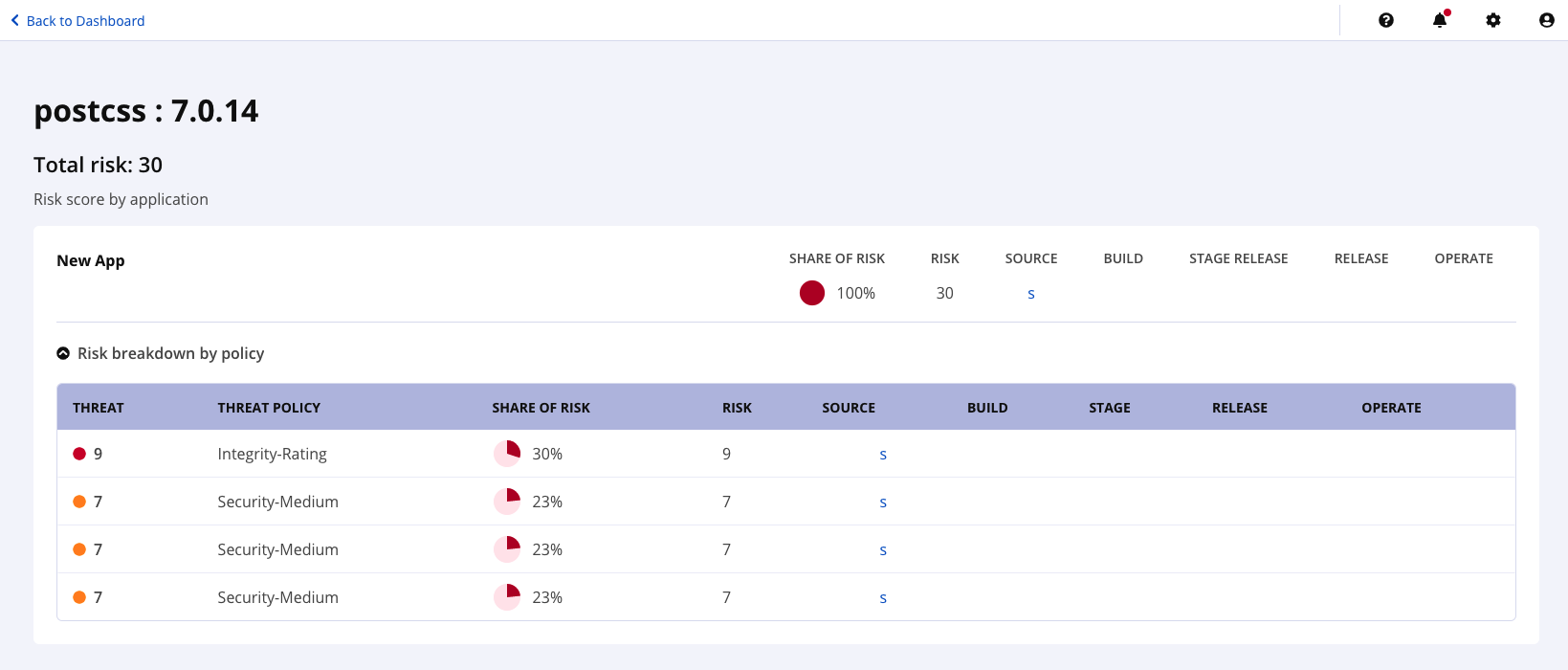 |
Exporting Components Data
For the components tab, all Risk columns are calculated by taking the associated Threat Level of the policy violation and multiplying it by the number of affected applications.
The columns exported into the file are:
Column Name | Column Value |
|---|---|
Component Name | The component that has active policy violations |
Affected Apps | The number of applications that have this component as a dependency |
Total Risk | Sum of the risk associated with the following columns |
Critical | Risk associated to the critical policy violations for the component |
Severe | Risk associated to the severe policy violations for the component |
Moderate | Risk associated to moderate policy violations for the component |
Low | Risk associated to the low policy violations for the component |
Applications View
The Applications view displays applications at risk based on any filters that have been set and the user's level of access. From this view, you can also access the latest reports for each stage that have been evaluated for the application.
As with components, risk is represented in a table with the ranges of Critical, Severe, Moderate, and Low. The values represent the number of unique policy violations at that severity level. The Total Risk column is calculated by summing all the values in the row, and the top, unlabeled row counts unique policy violations at that severity level across every application in the table.
Exporting Applications Data
For the applications tab, all Risk columns are calculated by taking the sum of the associated Threat Level of the policy violations of all affected components in the application.
The columns exported into the file are:
Column Name | Column Value |
|---|---|
Organization Name | The organization that owns the application |
Application Name | The application name |
Total Risk | Sum of the risk associated with the following columns |
Critical | Risk associated to the critical policy violations for the application. |
Severe | Risk associated to the severe policy violations for the application |
Moderate | Risk associated to the moderate policy violations for the application |
Low | Risk associated to the low policy violations for the application |
Waivers View
The waivers view shows all existing waivers applied at the same or higher hierarchy level, based on your filter selections.
This list can be filtered to show a customized waivers list that applies to specific organizations, applications, application categories, policy types, policy threat levels, and expiration dates (only available in the waiver view). Refer to the filter options for detailed descriptions of available filters.
It displays the waivers that meet the filter criteria. All columns of the waivers table in the dashboard can be sorted ascending or descending.
The Upgrade column indicates when an upgrade is available for a waived component. To configure monitoring for upgrades for waived components.
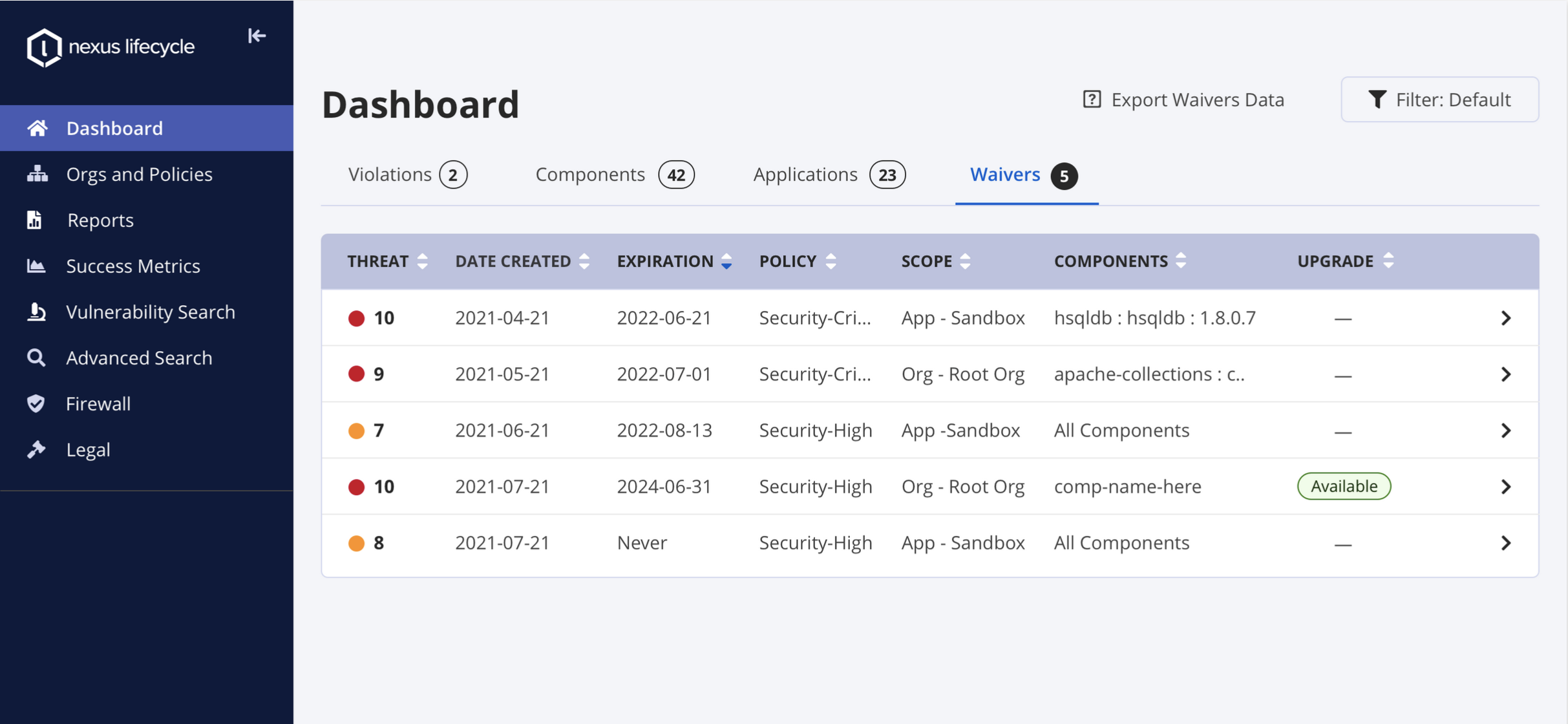 |
Click on a waiver to navigate to the waiver details pane. The waiver details pane includes:
The policy name on which the waiver is created
Name of the constraint, set for the policy
Conditions under which the policy is enforced. For security vulnerability-related policy waivers, click on the link to learn more about the vulnerability details.
Scope of the waiver
Components to which the waiver applies. The "Upgrade Available" tag will be displayed if monitoring for upgrades is configured and an upgrade is available.
Waiver expiration date
Username of the waiver creator
Waiver creation date
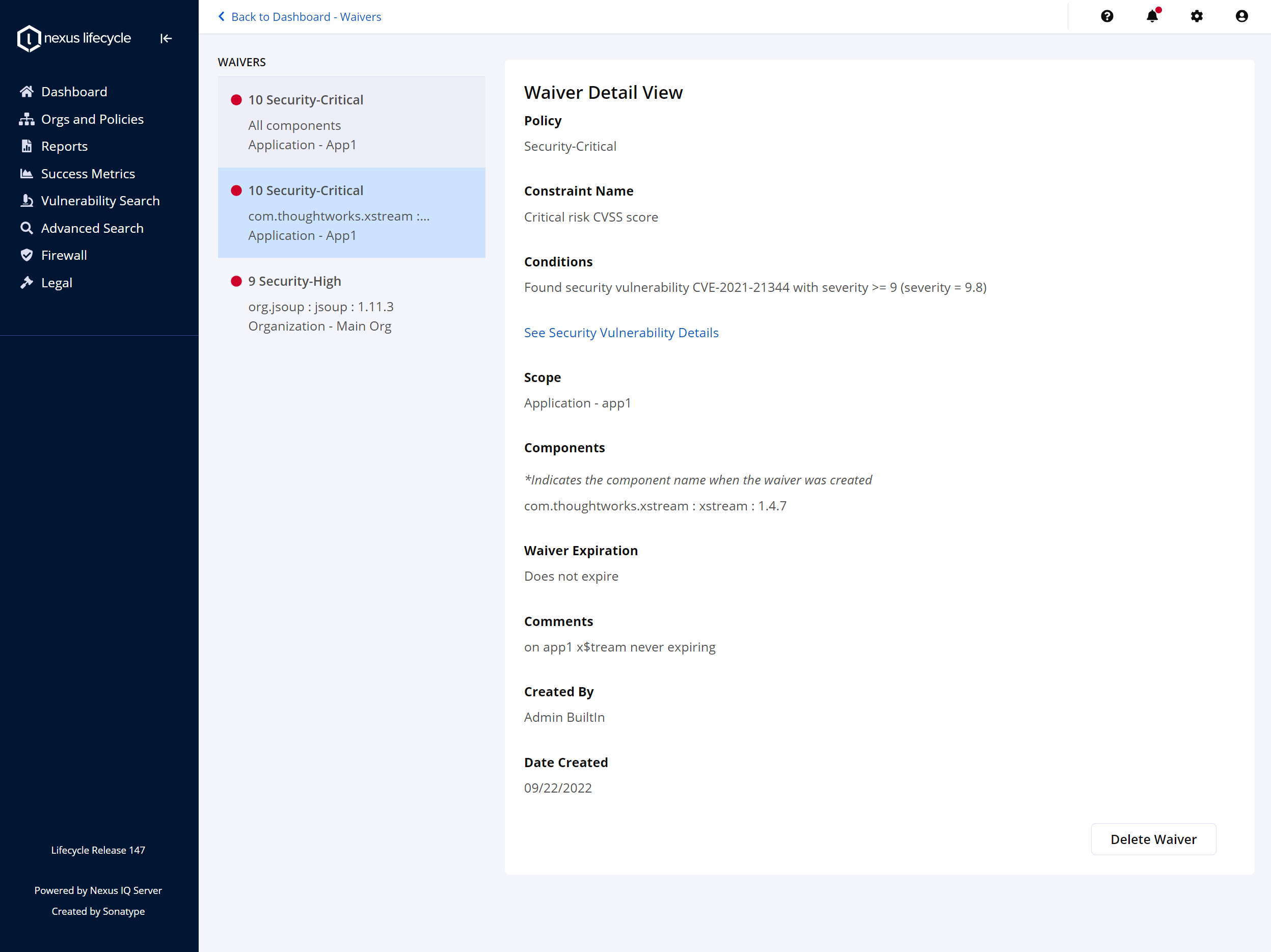 |
Select Export Waivers Data to download the waiver data to a CSV file.
Field name | Field value |
|---|---|
Waiver Id | Unique waiver ID generated by IQ server at the time of waiver creation |
Threat level | Threat level associated with the policy to be waived |
Created Date | Date of waiver creation (format yyyy-mm-ddThh:mm:ssZ 'T' is a quoted character and 'Z' represents UTC) |
Expiration Date | Date when the waiver is set to expire (format yyyy-mm-ddThh:mm:ssZ 'T' is a quoted character and 'Z' represents UTC) |
Policy Id | Unique policy ID generated by IQ Server at the time of policy creation |
Policy Name | Name of the policy to be waived (e.g. Security-critical, Integrity-Rating, Security-High etc) |
Policy Constraints | Conditions and constraints checked by the policy that is waived by this waiver |
Scope Type | The scope of the waiver determines whether the policy waiver will be applied to a specific org, application or repository. |
Scope Id | IQ server generated scope ID, useful for automation with REST APIs |
Scope Name | Organizational level at which the waiver is created. |
Component Match Strategy | Match strategy can be all components, all versions, or exact match. |
Component Hash | Unique component identifier |
Component Name | Name of the component associated with the policy that is waived by this waiver |
Upgrade | Indicates that an upgrade is available for the waived component. (Waived Component Upgrades must be configured.) |
Created by Id | Userid of waiver creator |
Created by Name | Username of the waiver creator |
Comment | Optional descriptive comments for the waiver |